A founder signs a software contract, integrates the platform into finance, sales, or operations, and moves on. Months later, the vendor hits distress, gets acquired, or stops supporting the product. Your team still depends on that software every day, but you may have no practical way to keep it running.
That problem sits at the center of many cross-border technology contracts. For businesses operating in New York and Ontario, software failure isn’t only a technical issue. It’s a continuity, contract, data, and enforcement issue. Mayo Law often sees this risk underestimated until a financing round, customer audit, or acquisition forces the question: if the vendor disappears, what exactly do you get, and how fast can you use it?
Software in escrow is one of the few tools built for that scenario. Used properly, it may reduce dependence on a single vendor without transferring the vendor’s intellectual property.
Introduction
If your company relies on a third-party application to process orders, manage customer records, or run internal workflows, a vendor failure may freeze far more than one software tool. It may interrupt payroll, compliance, client service, and reporting across two jurisdictions at once.
Software in escrow works like a business continuity backstop. A neutral third party holds critical software materials and releases them only if agreed trigger events occur. The idea is simple. If the vendor can’t or won’t keep the software operational, the customer may gain access to what is needed to maintain it.
For New York and Ontario companies, the legal value is only part of the picture. The practical value matters just as much. A vague escrow clause often gives false comfort. A well-built one addresses source code, build instructions, data dependencies, release mechanics, and cross-border enforcement before there’s a crisis.
What Is Software Escrow and Why It Matters

A home purchase gives a useful analogy. Funds don’t go straight from buyer to seller without conditions. A neutral party holds them until the deal closes properly. Software escrow applies the same logic to a different asset. Instead of money, the protected asset is the software package your business depends on.
What sits in escrow
In basic terms, software in escrow means a third-party escrow agent stores deposit materials for the benefit of the software customer. Those materials may include source code, documentation, scripts, database schemas, and other items needed to rebuild or support the application.
The arrangement matters because a software license alone usually doesn’t give you operational independence. You may have the right to use the product, but not the ability to maintain it if the vendor fails.
Practical rule: If your business can’t rebuild, host, or support the application after release, your escrow is probably too narrow.
Why businesses are using it more often
The market itself shows how central this issue has become. The global software escrow services market was valued at $3,848.91 million in 2021 and is projected to reach $6,793.8 million by the end of 2025, with North America holding 42.55% of global revenue share, according to the software escrow services market report.
That growth tracks what founders already know. Modern companies rent critical infrastructure from vendors all the time. A strong escrow clause may matter to:
- Founders raising capital because investors often test concentration risk and continuity planning
- SMEs signing enterprise contracts because larger customers may ask what happens if a core supplier fails
- Buyers in M&A because diligence often turns on whether key systems can survive a vendor disruption
- Regulated businesses because continuity and resilience concerns don’t stop at the software license
The three-way balance
A good escrow deal is not anti-vendor. It balances interests.
The vendor protects its IP by placing materials with a neutral party under strict release conditions. The customer gains a limited, conditional path to continuity. The agent administers the process without taking sides.
What works is a clause tied to a real operational risk. What doesn’t work is treating escrow as symbolic language buried near the end of a license agreement.
The Key Players in an Escrow Agreement
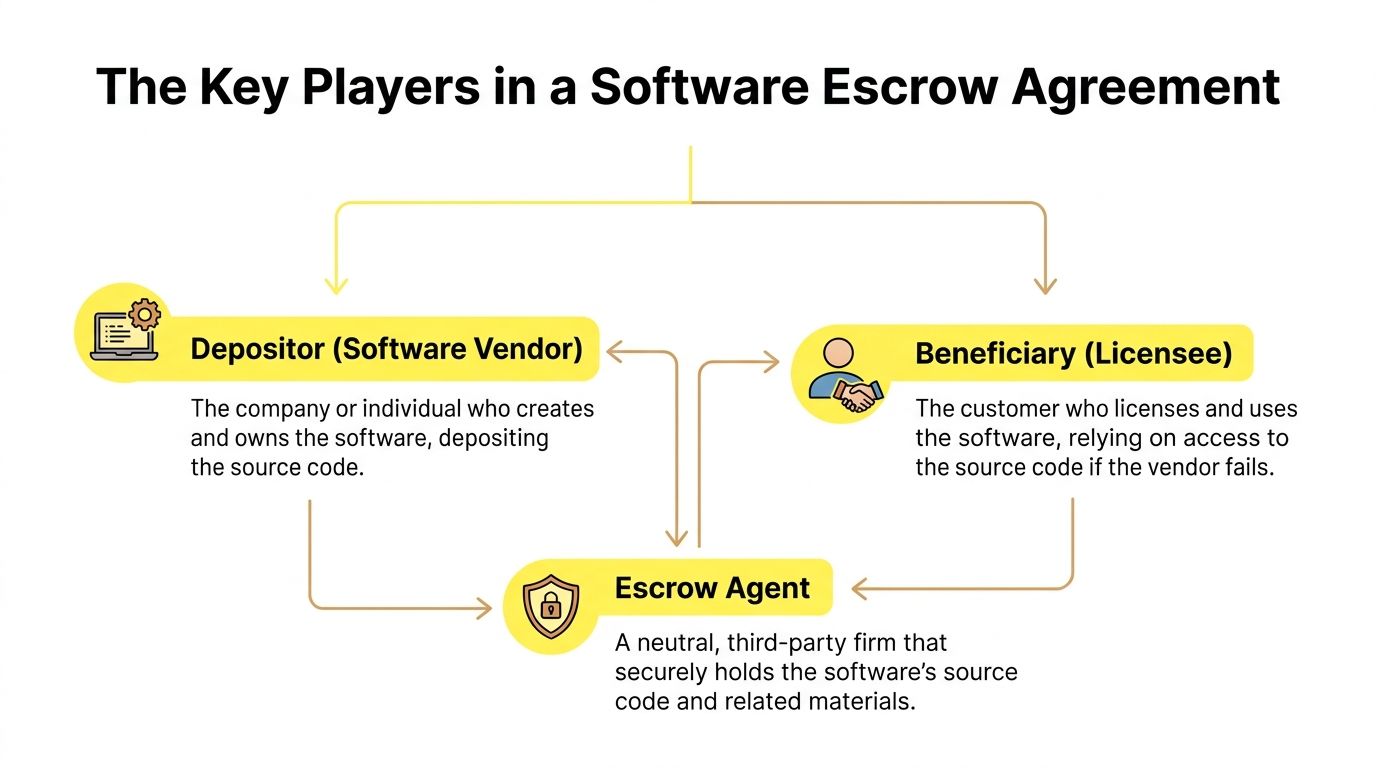
Most strong arrangements use a tripartite agreement. That means all principal players sign the same contract, rather than relying on side promises.
Depositor
The depositor is usually the software vendor or developer. This party owns or controls the code and has the practical ability to assemble the deposit package.
Its obligations should be explicit. A vendor that promises only to deposit “source code” may leave out the very items needed to make that code useful.
Checklist items to review for the depositor include:
- Update duties. How often must the vendor refresh the deposit?
- Scope of materials. Does the deposit include scripts, dependencies, keys, and documentation?
- Format requirements. Is the material delivered in a usable and organized form?
- Representations. Does the vendor confirm it has the right to deposit the materials?
A related contract concept appears in other transactions too. Priority rights and future transfer rights can become just as important as present rights, which is why careful drafting matters in deals involving right of first offer provisions.
Beneficiary
The beneficiary is the customer or licensee that depends on the software. This party is not buying ownership of the code. It is negotiating a conditional right to access and use the deposit if a release event happens.
The beneficiary should focus less on labels and more on function. Ask a simple question. If the release occurs on a Friday afternoon, what exactly would your internal team or outside developer receive on Monday morning?
The legal right to receive code is much less valuable than the operational ability to run it.
Escrow agent
The escrow agent is the neutral custodian. In a strong arrangement, the agent does more than store files. It administers deposit procedures, release requests, and sometimes verification.
Look closely at these clauses:
- Release process. How does the agent evaluate a release request?
- Notice mechanics. Who gets notice, and how much time is allowed to object?
- Security controls. How are deposited materials stored and protected?
- Liability limits. What responsibility does the agent accept if something goes wrong?
A weak contract often names the parties correctly but leaves their duties blurry. That usually creates friction when timing matters most.
Structuring Your Software Escrow Agreement
Most escrow disputes start with drafting shortcuts. The agreement sounds protective until someone asks for release and discovers the contract doesn’t define the trigger, the deposit, or the post-release rights with enough precision.
Clauses that deserve close attention
Use this review list before signing:
- Deposit materials. Don’t stop at “source code.” For many applications, the useful package may also include build instructions, test scripts, APIs, database structures, credentials handling procedures, and deployment materials.
- Release conditions. Common triggers may include insolvency, failure to support, failure to maintain, or other agreed breakdowns in service.
- License after release. The contract should state what the beneficiary may do with the released materials. Usually that means limited use for continuity, not a transfer of ownership.
- Dispute mechanism. If the vendor contests release, the contract should spell out the path for resolving that dispute.
- Timing. Slow release language can undermine the whole point of escrow.
Anyone who has negotiated acquisition documents will recognize the pattern. The words that look routine often decide the practical result later, just as they do in stock purchase agreements.
Why verification isn’t optional in serious deals
A 2009 Iron Mountain survey found that 66% of escrow deposits are incomplete and 92% require additional input from programmers to become usable, according to Iron Mountain’s technology escrow verification survey release.
That finding still captures the main drafting problem. Businesses often negotiate for release rights but fail to negotiate for a usable deposit.
What works better is matching verification to the importance of the software:
- Basic review may fit low-dependency tools where continuity risk is limited.
- Intermediate verification may make sense where the software supports a core workflow and environment compatibility matters.
- Full technical verification is often the better fit where a shutdown would materially disrupt operations.
Cost and leverage
Escrow has a cost, but the bigger issue is allocation. Vendors often accept storage and deposit responsibilities more readily than intensive verification. Customers often push for verification because they bear the continuity risk.
That negotiation usually improves when both sides treat escrow as a narrow resilience tool rather than an attempt to seize IP. If the agreement is framed as continuity insurance, deals tend to move faster.
Understanding Verification and Maintenance Options
The most common mistake in software in escrow is assuming that a deposited archive equals recoverability. It doesn’t. Code can be old, incomplete, incompatible, or impossible to build in your environment.
What verification actually tests
Technical verification typically includes completeness reviews, compatibility testing, and functionality validation, and Codekeeper’s software escrow guide notes that unverified deposits can lead to 40-60% failure rates in reconstruction efforts post-release.
That matters because a release event is usually already a stressed moment. Your company won’t want to discover then that a missing dependency breaks the build.
A deposit that can’t be compiled or deployed is storage, not protection.
Software Escrow Verification Levels Compared
| Verification Level | What It Includes | Best For |
|---|---|---|
| Basic inventory | Confirms the listed materials were deposited | Lower-risk software or early-stage contracts |
| Compatibility review | Checks whether the materials align with the intended environment | Applications with important operational dependencies |
| Full build and functionality testing | Attempts to build and validate the application in a controlled setup | Mission-critical software where downtime risk is serious |
Maintenance matters as much as verification
Even a good verification exercise loses value if the deposit goes stale. This issue appears often with frequent product updates, API changes, and cloud dependencies.
A practical maintenance process usually addresses:
- Refresh schedule based on releases or agreed intervals
- Change tracking so both sides know what version is on deposit
- Testing cadence for higher-risk systems
- Responsibility split between vendor updates and beneficiary review
Traditional escrow doesn't map neatly onto SaaS
For cloud products, "give me the source code" is often the wrong question. The better question is what package would let your business continue operating if the service stops.
That may include environment details, database structures, deployment logic, and operational documentation. Without those pieces, even verified source code may not restore a working service.
Special Considerations for SaaS and Cloud Services
Classic escrow language was built around on-premise software. SaaS changes the problem because the customer usually depends on a running service, not just a codebase.
Why standard clauses fall short
Standard escrow agreements are often inadequate for SaaS because continuity may require access to hosting environments, databases, and configurations, and cross-border use raises data sovereignty concerns under laws such as PIPEDA in Canada and CCPA in the United States, as discussed in Lewis Silkin's analysis of software escrow and SaaS.
For a New York and Ontario business, that creates a double layer of risk. You may need the materials to run the application, and you may need a compliant path to move or access data across borders.
What a SaaS escrow package may need
A practical SaaS escrow package often reaches beyond source code. Depending on the product, parties may want to consider:
- Application materials such as source code, scripts, and technical documentation
- Environment details covering hosting setup, infrastructure dependencies, and configuration
- Data continuity terms addressing backups, export rights, and usable formats
- Third-party services identifying critical integrations and access dependencies
These issues overlap with IP risk. If a vendor dispute also touches proprietary technology, broader strategy may matter, including advice from a patent infringement attorney where ownership and use rights are contested.
Jurisdiction changes the practical answer
The SaaS question isn't just what goes into escrow. It's also where the data sits, who controls credentials, and what laws apply to access after release.
That's why a cloud escrow clause drafted without cross-border enforcement language often underperforms. It may promise access in theory while leaving the customer blocked by missing approvals, conflicting privacy obligations, or vendor-controlled infrastructure in practice.
Navigating Cross-Border Escrow Between the US and Canada
A software escrow clause that works within one jurisdiction may still fail across the border. New York and Ontario businesses should think beyond the deposit itself and address how the agreement gets enforced if a dispute arises.
Questions founders and in-house teams should ask
Start with these:
- Which law governs the agreement. New York law, Ontario law, or another forum?
- Where are disputes resolved. Court, arbitration, or a staged process?
- What documents need formal execution. In some deals, notary formalities, certifications, or apostille coordination may matter for related enforcement steps.
- How quickly can release happen across borders. Delay may be more damaging than the dispute itself.
Cross-border dispute planning is often stronger when parties address forum and enforcement early, including whether arbitration in Canada and enforcement considerations may fit the transaction better than court litigation.
Cross-border escrow is only partly about storage. The harder question is whether your release right can be exercised fast enough to matter.
New pressure from AI systems
Escrow is also expanding beyond conventional code. The Society for Computers and Law discussion of software escrow and AI notes that escrow for AI models is becoming important because the protected materials may include proprietary datasets and model weights, not only source code.
For a company operating between the U.S. and Canada, AI raises distinct issues:
- Export and regulatory limits may affect what can be transferred
- Training data rights may be separate from software rights
- Model reproducibility may depend on workflows the vendor never documented for release
- Audit trails may matter if regulators, customers, or buyers later ask how the model was built
Practical cross-border checklist
Use this as a working list for vendor discussions:
- Identify the business-critical application.
- Define the release events in operational language, not only legal labels.
- Confirm where the deposit will be held and under what governing law.
- Check whether the release package is usable in New York and Ontario operations.
- Review whether privacy, data transfer, or sector rules could complicate release.
- Ask what formal execution steps might support enforcement if a dispute arises.
A Practical Checklist for Your Business
Founders usually don't need a perfect escrow package for every vendor. They do need to identify which relationships create real continuity risk.
Key considerations
- Map your critical vendors. Which application would disrupt revenue, compliance, or service delivery if support stopped?
- Define the minimum usable package. Ask what your replacement developer would need on day one after release.
- Match verification to criticality. Low-risk tools and mission-critical systems usually shouldn't get the same treatment.
- Review update discipline. A strong deposit that never gets refreshed may become outdated quickly.
- Address SaaS realities. If the software runs in the vendor's cloud stack, confirm the agreement covers what continuity requires.
- Check cross-border enforceability. A release right is only as useful as the process behind it.
- Separate continuity from ownership. Escrow usually protects operations, not a transfer of underlying IP.
- Test the business case. If a board member, investor, or acquirer asked why escrow was omitted, would your answer sound disciplined?
What tends to work
The strongest arrangements are usually narrow, specific, and tied to a real dependency. They define trigger events clearly, identify the full deposit package, and assign verification in a way that matches the business risk.
What tends not to work
The weakest arrangements rely on a one-line clause in a master services agreement, leave "deposit materials" undefined, or ignore the cloud environment entirely. Those contracts often look fine until the vendor relationship breaks down.
Build Your Business on Solid Legal Ground
A well-structured software in escrow arrangement may protect more than code. It may protect continuity, bargaining power, and deal value when a vendor relationship becomes unstable. For businesses operating in Ontario and New York, the drafting needs to reflect cross-border reality, not just a template.
Mayo Law advises startups and SMEs on technology contracts, growth-stage risk, and cross-border business planning. If you're building operations across the U.S. and Canada, the broader legal foundation matters too, including early-stage entity planning such as an Ontario incorporation checklist.
If you're evaluating software in escrow for a cross-border business, Mayo Law may help you assess the contract, the jurisdiction issues, and the practical continuity risks. Schedule a consultation to discuss your business needs.
LEGAL DISCLAIMER: The information provided in this article is for general informational and educational purposes only and does not constitute legal advice. Reading this article, visiting mayo.law, or contacting Mayo Law does not create an attorney-client relationship. The content of this article should not be relied upon as a substitute for professional legal counsel suited to your specific circumstances. Legal outcomes depend on the particular facts and circumstances of each individual case, and no attorney can guarantee a specific result. Laws, regulations, and legal procedures are subject to change and may vary by jurisdiction. If you require legal assistance, you should consult with a qualified attorney licensed to practice in the relevant jurisdiction. Mayo Law expressly disclaims any and all liability with respect to actions taken or not taken based on the contents of this article.