It usually starts with a resignation, a suspicious download, or a competitor whose pricing suddenly looks too familiar.
By the time a founder calls counsel, the problem is rarely theoretical. An employee has left with files, a vendor has reused internal know-how, or a Canadian affiliate has received material that was originally shared under a U.S. NDA. The first questions are practical ones. What was taken, who touched it, and where did the misuse happen?
Trade secret misappropriation is the improper acquisition, use, or disclosure of confidential business information. The legal label matters, but the business problem comes first. Revenue can move fast. Customers get approached. Product timelines slip. Internal investigations pull managers and engineers off real work.
The cross-border piece makes these disputes harder than many founders expect. A company may be based in California, keep developers in Ontario, store documents on U.S. servers, and sell through a Canadian subsidiary. That mix creates real friction over forum, governing law, evidence collection, and enforcement. A U.S. injunction does not automatically solve a Canadian misuse problem, and a weak confidentiality process in either country can hurt the claim from the start.
That is why prevention and proof have to work together. Good agreements help, but so do access controls, clean departure procedures, and records that show what was confidential and who had access to it. Founders weighing secrecy against public filing should also understand the trade-offs between confidential know-how and registered rights, including the differences explained in this guide on trade secret vs. patent protection.
In practice, the hardest fights are often about discipline. Can the company show that it treated the information as secret, trace the movement of files, and move quickly enough to contain the damage in both the United States and Canada? Those answers often decide whether the claim has real settlement value or turns into an expensive lesson.
What Qualifies as a Protectable Trade Secret
A founder often learns this point after a problem starts. The company loses an engineer in Toronto, a salesperson in Chicago starts calling the same accounts, and everyone says the team took "our secrets." In court, that label only helps if the information meets the legal standard in the first place.

A protectable trade secret is information that has business value because it is not generally known or readily ascertainable, and the company has kept it confidential. That basic idea shows up in both U.S. and Canadian cases, even though the procedural routes and remedies can differ. For cross-border businesses, that overlap matters. If the same dataset is loosely shared by a U.S. parent and a Canadian affiliate, the weakness will travel with the claim.
What usually counts
Courts commonly treat these categories as capable of protection:
- Technical know-how: source code, build processes, formulas, manufacturing methods, internal testing protocols.
- Commercial information: customer lists built from non-public inputs, pricing models, margins, supplier terms, bid strategy.
- Operational information: launch timing, product roadmaps, internal playbooks, and failed R&D results that reveal what does not work.
The harder cases are often the most valuable ones. A customer list is not protected just because it took time to assemble. It becomes stronger as a trade secret when it includes buying history, pricing sensitivity, renewal timing, decision-maker contacts, and other non-public detail a competitor could not gather quickly on its own. The same is true for internal quoting tools, prompt libraries, data-labeling methods, or a process improvement that saves six minutes per unit on a production line.
What usually does not count
Trade secret law does not give a company ownership over everything an employee knows.
These categories usually fall outside protection:
- General skill and experience: sales ability, coding skill, management judgment, industry familiarity.
- Public or easy-to-find information: website content, public filings, openly available pricing, standard methods.
- Information with weak controls: shared folders open to everyone, unrestricted downloads, documents passed around without confidentiality terms.
That last category causes a lot of damage in real disputes. Courts look closely at how the company handled the information before the alleged theft. A "confidential" label helps, but it carries limited weight if dozens of employees had unrestricted access, contractors were not under signed agreements, or a Canadian subsidiary could copy files from a U.S. server without any approval trail.
Practical rule: If you cannot show who had access, why they had it, and what restrictions applied, the information may be valuable but still fail as a trade secret.
The most important test is behavior
Secrecy is not inherent. It is maintained through process.
Start with five questions:
- Who can access the information right now?
- Is access limited to a business need?
- Do you keep logs or other records showing who opened, downloaded, or sent it?
- What happens to devices, credentials, and cloud access when someone leaves?
- Do your contracts clearly cover confidentiality, ownership, permitted use, and return or deletion of materials?
These points matter even more in U.S.-Canada operations because the evidence is often split. Employment agreements may be signed in Ontario, product repositories may sit on U.S. infrastructure, and the alleged use may happen through a different affiliate. If the company cannot prove consistent treatment of the information across both sides of the border, defense counsel will argue that the material was ordinary business information, not a protected secret.
Founders also need to choose between secrecy and public filing with care. If a product can be reverse engineered once it ships, trade secret protection may be fragile from day one. If the value lies in internal process, confidential methods, or know-how that stays behind the scenes, secrecy may offer a longer runway. This comparison of trade secret vs patent protection is a useful starting point for that decision.
One final point. Trade secret disputes usually come from people with legitimate access, not movie-style external theft. Former employees, contractors, distributors, and joint venture partners create the most common fact patterns. In a cross-border business, those relationships also create the proof problem. The same person may have touched the information lawfully in one country and misused it in another, which is why clear documentation of scope, access, and restrictions matters from the start.
Legal Standards for Misappropriation in the US and Canada
A startup operating in New York and Ontario may feel like it's dealing with one business problem. Legally, it's often dealing with two systems that approach the same conduct differently.
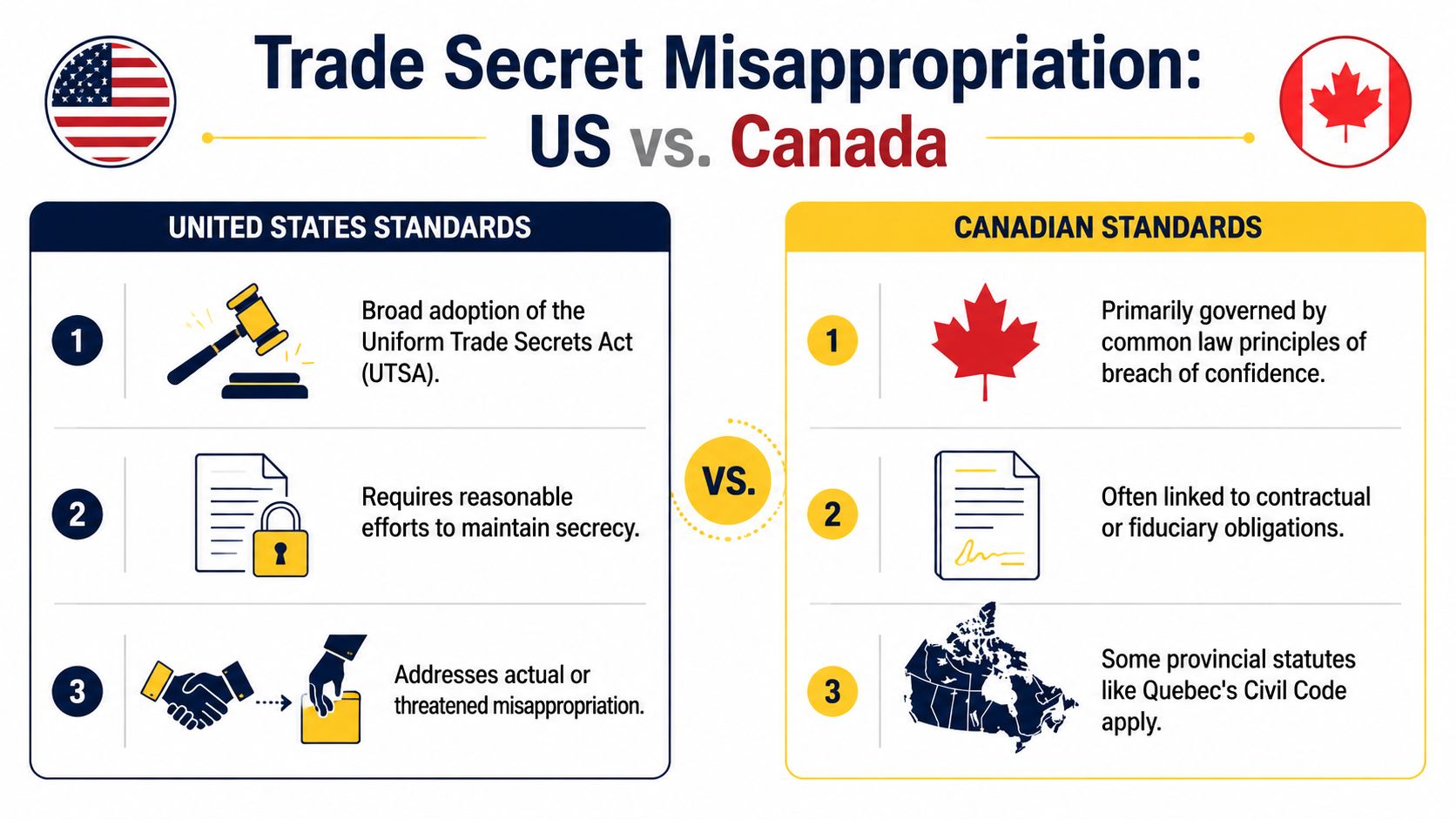
The U.S. approach
In the United States, the framework usually starts with the federal Defend Trade Secrets Act and, depending on the state, a version of the Uniform Trade Secrets Act. The core proof points are fairly consistent.
A plaintiff generally needs to show:
| Issue | What the court looks for |
|---|---|
| A real trade secret | Information with independent economic value because it isn't generally known or readily ascertainable |
| Reasonable secrecy measures | NDAs, restricted access, password controls, logs, training, document handling rules |
| Misappropriation | Improper acquisition, disclosure, or use |
The second element is where many claims weaken. In New York and under the DTSA, a successful claim requires proof that the information was a trade secret, that the owner took reasonable protective steps, and that it was improperly acquired or used. Courts often reject claims where those protective steps aren't documented, and 70% of failed claims cite inadequate protections, according to Trestle Law's summary of trade secret litigation requirements.
That doesn't mean a startup needs enterprise-grade bureaucracy. It does mean a judge wants something tangible: signed agreements, access restrictions, policies, logs, and evidence that the company acted like the information mattered.
The Canadian approach
Canada does not have a single national trade secret statute equivalent to the U.S. federal DTSA. In Ontario and other common law provinces, the claim often proceeds through breach of confidence, contract, fiduciary duty, or related common law principles.
The Canadian analysis usually turns on questions like these:
- Did the information have a confidential quality?
- Was it shared in circumstances importing an obligation of confidence?
- Was it used or disclosed without authorization to the owner's detriment?
The practical difference is important. In the U.S., businesses often frame the issue through statutory trade secret language. In Canada, the surrounding relationship can carry more weight. Employment duties, partnership arrangements, board access, consultant relationships, and fiduciary obligations may become central.
Where founders get into trouble
The legal tests sound manageable until the facts span both sides of the border.
A common example looks like this:
- A U.S. parent shares pricing logic with a Canadian distributor.
- The parties sign a short NDA with no governing-law clause.
- A key employee leaves and joins a competitor in Ontario.
- The company wants a U.S. court order to stop use immediately in Canada.
That plan may stall quickly. The U.S. claim might be strong, but the Canadian court will still ask what obligations existed under the actual relationship, what the contract says, and whether the relief sought should be recognized locally.
The same misconduct can support a strong U.S. claim and still require different pleadings, evidence, and remedies in Ontario.
What works better than a generic NDA
Founders often rely on one broad confidentiality form for employees, contractors, advisors, and cross-border partners. That's convenient, but it often creates proof problems later.
A better approach is to match the document to the relationship:
- Employment agreements should address confidentiality, ownership, return of property, and post-departure cooperation.
- Contractor agreements should clarify that work product and embedded know-how belong to the company.
- Commercial NDAs should define confidential information carefully and deal with permitted use, storage, and compelled disclosure.
- Cross-border agreements should state governing law, forum, and enforcement expectations.
The law rewards clean records. If your contracts, access controls, and internal practices tell the same story, a court is much more likely to treat the information as protectable and the conduct as misappropriation.
How to Prevent Trade Secret Misappropriation
A startup can do almost everything right on product and still lose control of its edge through ordinary operational gaps. The usual pattern is familiar. Source code sits in a shared repository, pricing logic lives in a sales folder, key customer notes are spread across personal devices, and the company assumes a signed NDA will clean up the risk later. It usually does not.
Prevention has to do two jobs at once. It must reduce the chance of misuse, and it must create proof you can use if the dispute lands in a U.S. or Canadian court. Cross-border cases expose weak systems quickly. A founder may assume a U.S. injunction will solve the problem, but if the actor, devices, or business activity are in Canada, the record still has to show what information was protected, who had access, and what rules applied to that person.
Contract controls
Contracts still matter. They just need to match the relationship and the actual flow of information.
The documents that hold up best usually include:
- Clear confidentiality definitions: identify categories of protected information with enough precision that a court can tell what is secret.
- IP assignment language: cover employees, developers, consultants, and advisors who may create code, models, documentation, or process improvements.
- Use restrictions: state what the recipient may do with the information, not just what they cannot disclose.
- Return, deletion, and certification terms: require the departing person or vendor to return property, delete copies where permitted, and confirm the steps taken.
- Cross-border dispute terms: address governing law, forum, service mechanics, and cooperation obligations if evidence or parties are split between the U.S. and Canada.
A short NDA helps at the start of a conversation. It does not fix ownership gaps, unclear contractor status, or a departure where the person had months of broad system access.
Technical controls
Courts look at behavior, not just paperwork. If a company says its data is highly confidential but stores it in one open drive with no logging, that inconsistency hurts.
The practical controls are rarely exotic:
- Need-to-know access: limit repositories, deal files, pricing models, and product roadmaps to the people who need them.
- Logging and retention: configure systems so access history, downloads, forwarding activity, and version changes are preserved.
- Segmentation: separate source code, customer information, financial models, and strategic plans instead of keeping everything in one place.
- Device and account controls: use company-managed devices where possible, restrict external storage, and disable accounts immediately at exit.
- Vendor discipline: check where cloud providers store data and whether logs can be collected promptly if a dispute starts in another jurisdiction.
Founders face a real trade-off here. Tight controls can slow a small team. Loose controls make litigation harder and often more expensive. The better answer is targeted restriction around the information that would matter most to a competitor, not blanket friction on every file.
For software companies, continuity planning also needs care. An escrow arrangement can reassure customers without giving away more than necessary, but the release conditions, deposit scope, and confidentiality terms must line up with the company's trade secret strategy. A properly structured software escrow arrangement can help on the commercial side while preserving the argument that the code remains confidential.
Policy and training
Policies fail when they read like a handbook no one uses. Useful policies tell people exactly what counts as confidential information, where it may be stored, which tools are approved, how information may be shared with customers or contractors, and what happens on resignation or termination.
Managers need separate guidance. They are usually the first to see warning signs such as unusual downloads, requests for broader access, side-channel communications with a competitor, or resistance to return-of-property steps at exit.
Training also has to reflect local law and local practice. A U.S. company with engineers in Ontario should not assume its standard U.S. onboarding and offboarding scripts are enough. The contract language, privacy rules, device practices, and enforcement path may look different once a Canadian employee or contractor is involved.
What a useful audit looks like
A good audit is operational. It does not ask only whether the company has signed NDAs. It asks whether the business can prove control.
Start with five questions:
- What information would cause real competitive harm if it left the company?
- Where does that information live, including backups, chat systems, and personal-device spillover?
- Who can access it today, and who accessed it in the last few months?
- Which contract and policy terms apply to each group with access?
- What evidence could be collected quickly if misuse started in the U.S. but the person or activity was in Canada, or the other way around?
That last question is the one many guides miss. In a domestic dispute, weak records are bad. In a cross-border dispute, they can decide the case. If servers are in one country, the employee is in another, and the customer impact appears in both, counsel will need a clean chain of documents, logs, and witness evidence to move quickly.
Mayo Law works with businesses across the GTA and on cross-border matters. Joseph Mayo is licensed in Ontario and New York, so companies with U.S. ties can coordinate contracts, risk reviews, and dispute planning in one place rather than splitting the work by jurisdiction.
Steps for Investigating and Litigating a Claim
Trade secret disputes usually don't begin with certainty. They begin with suspicion.
A founder notices unusual downloads before a resignation. A customer says a rival knows details that should not be public. A former contractor suddenly launches a product that looks too similar, too quickly. The first response should be controlled, not emotional.
First 72 hours
The early move is preservation.
That often means:
- Locking down accounts: suspend deletion rules and preserve cloud data.
- Securing devices: company laptops, phones, external drives, and shared repositories.
- Capturing logs: email forwarding rules, login history, file access events, USB activity where available.
- Limiting internal chatter: keep the review within a small team so evidence isn't altered and legal strategy isn't undermined.
Founders sometimes confront the suspected person immediately. That's understandable, but it can backfire. It warns the other side, gives them time to wipe devices, and may turn a recoverable problem into an evidentiary fight.
Building the factual record
A solid case usually relies on chronology. Who had access, when they had it, what they downloaded, where they went next, and how the information appears in the competitor's hands.
A practical investigation may involve counsel, HR, IT, and an outside forensic team. The job isn't just to confirm that files moved. The job is to connect the movement to actual protected information and resulting misuse.
Consider two anonymized examples.
A Toronto software company discovers that a departing product lead copied roadmap files and customer migration notes before joining a New York rival. The company's access logs and signed agreements are clean. It can move quickly.
A manufacturing supplier with operations in Ontario and upstate New York suspects a distributor leaked bid models to a competitor. But the pricing files sat in an unrestricted folder and the distributor agreement uses generic confidentiality language. The business may still have a claim, but proving the scope and legal status of the information gets harder.
The strongest litigation file is usually built before the cease and desist letter goes out.
When litigation starts
Once the facts are sufficiently developed, counsel may send a demand letter, seek negotiated safeguards, or move directly for court relief. The right choice depends on urgency, proof, and whether continued use is likely.
Emergency relief can be critical. If the other side is using source code, customer pricing, or deal strategy in an active sales cycle, waiting may cause damage that money won't fully repair. Related issues can overlap with other IP claims too, especially where copied technology may support more than one theory. In some matters, it's worth understanding how trade secret claims interact with patent infringement disputes.
Litigation then becomes a proof exercise. Define the secret precisely. Show the protection measures. Prove the acquisition, use, or disclosure. Keep the evidence chain clean.
Available Remedies and Calculating Damages
The first remedy most businesses need is not money. It's a court order that stops the bleeding.

Injunctions
An injunction can prohibit use, disclosure, transfer, or retention of the trade secret. In a departure case, it may also restrict the use of company devices, require return of materials, or preserve forensic evidence.
This is often the practical objective in the early stage. A startup can survive a damages fight later. It may not survive months of uncontrolled use by a better-funded competitor.
In cross-border settings, however, founders need to remember a hard truth. Winning relief in one country doesn't mean the remedy automatically works in the other. That issue becomes especially important in the next section.
The three common damages models
Damages in trade secret misappropriation cases are commonly measured in one of three ways:
| Damages model | Core idea |
|---|---|
| Plaintiff's losses | What the owner lost because of the misappropriation |
| Defendant's unjust enrichment | What the wrongdoer gained from using the secret |
| Reasonable royalty | What a hypothetical license would have cost at the time of misuse |
Courts may use whichever measure best fits the evidence. If direct losses are hard to prove, a royalty model may become more realistic.
According to Altolit's discussion of trade secret damages, courts often use a hypothetical negotiation framework when setting a reasonable royalty, and one California court upheld a royalty for the full period of misuse even though the secret later became public, placing the uncertainty risk on the defendant.
Why damages work often goes wrong
Many businesses know they were harmed but cannot explain the harm in a way a court can use. The evidence may show copying, but not the value of what was copied, how it changed the market, or what portion of profit flowed from that particular information.
That is why damages analysis should begin early, not after discovery closes.
Useful materials often include:
- Financial records tied to the secret
- Comparable licenses or internal valuation documents
- Development cost records
- Sales timelines before and after the misuse
- Expert analysis that isolates the value of the specific information at issue
A damages theory that sounds fair in a boardroom can still fail in court if it doesn't tie dollars to the precise trade secret that was misused.
Other relief
Depending on the facts, courts may also award enhanced damages or attorney's fees for willful misconduct under applicable law. But those remedies usually depend on proof of especially blameworthy conduct. They should be treated as potential upside, not the foundation of the case.
Cross-Border Enforcement Between the US and Canada
Your U.S. counsel gets a fast injunction against a former employee. The order looks strong. Then you learn the employee lives in Ontario, the laptop is there, the new employer is there, and the documents you need sit with a Canadian cloud administrator. At that point, the fundamental question is not whether you can win on paper. It is whether you can make the remedy matter in both countries.
That gap catches founders by surprise. Many guides explain how to prove a trade secret claim in one court. Fewer address what happens when the defendant, evidence, and business harm are split between the United States and Canada.
The legal theories overlap, but the enforcement path does not. In the United States, a plaintiff may rely on the Defend Trade Secrets Act and related state-law claims. In Canada, the claim often turns on breach of confidence, contract, fiduciary duty, or other common law and equitable principles. Those differences affect where you sue, what interim relief is available, how you describe the secret, and whether a U.S. order will be enough by itself.
A common fact pattern looks like this. A Delaware startup hires a software engineer in Ontario. The engineer works remotely, accesses U.S.-hosted repositories, leaves, and joins a Toronto competitor. The startup files in U.S. federal court because the contract selects New York law and the servers are in the United States.
That may be a sound first move. It may also be incomplete.
Questions usually surface fast:
- Will a Canadian court need to recognize or supplement the U.S. order before local enforcement becomes practical?
- Does the agreement require litigation in one forum, or does it leave room for parallel proceedings?
- Are the confidentiality and return-of-property obligations drafted broadly enough to cover cloud accounts, personal devices, and post-employment use?
- Will the facts fit both a U.S. trade secret claim and a Canadian breach of confidence theory?
I usually tell cross-border clients to treat forum, governing law, and enforcement mechanics as one package. A clean contract helps, but it does not erase local procedure, local evidence problems, or local limits on employment-related restraints. A U.S. injunction against an Ontario resident can be useful. It is not self-executing in Ontario.
That is why the forum selection clause in your cross-border agreements deserves the same attention as the NDA definition itself. If the clause is vague, permissive when it should be exclusive, or disconnected from where the people and assets are, you may spend the first phase of the dispute fighting about venue instead of stopping the misuse.
Canadian remedies can also differ in ways that matter strategically. In some cases, Canadian courts may focus on the unfair competitive head start gained from the misuse, often discussed as springboard relief. That concept can be useful where the defendant used confidential know-how to shorten development time or enter the market sooner, even if the plaintiff's direct lost-profit model is hard to prove.
The practical lesson is simple. Cross-border trade secret enforcement requires a two-country plan from the start. If your contracts, evidence preservation steps, and injunction strategy work only in the United States or only in Canada, the defendant will use that gap.
Client Checklist and Sample Contract Clauses
A founder doesn't need a fifty-page policy to improve their position this week. They need a short checklist and contracts that say what the company expects.
Trade secret audit checklist
Use this as a starting point:
- List the assets: identify source code, pricing data, customer lists, formulas, playbooks, vendor terms, and internal models worth protecting.
- Map access: record who can view, copy, export, and share each category.
- Review agreements: confirm employees, contractors, advisors, and partners have signed current confidentiality and IP ownership terms.
- Check offboarding: make sure departure procedures cover devices, credentials, cloud folders, notes, and acknowledgments.
- Preserve proof: confirm your systems retain useful access records and document history.
- Test the cross-border piece: check governing law, forum, and enforcement language for U.S.-Canada relationships.
Sample clauses in plain English
Confidential information clause
"Confidential Information includes non-public technical, commercial, financial, and operational information disclosed by the Company, including customer data, pricing, source code, product plans, business methods, and related analyses."
This avoids the mistake of defining confidentiality too vaguely.
Use restriction clause
"The Recipient shall use Confidential Information solely for the permitted business purpose and shall not disclose it except to personnel who need to know it and are bound by written confidentiality obligations."
This ties disclosure to a specific purpose and a controlled audience.
Return and deletion clause
"Upon request or termination of the relationship, the Recipient shall promptly return or securely destroy Confidential Information and certify compliance in writing, except where retention is required by law."
This creates a clean end point and a paper trail.
For employment agreements, dispute planning should also consider whether court litigation, arbitration, or a hybrid approach fits the relationship. These issues often overlap with arbitration agreements in employment contracts, especially where confidentiality and injunctive relief need to work together.
Frequently Asked Questions
| Question | Answer |
|---|---|
| What is trade secret misappropriation? | It is the improper acquisition, use, or disclosure of confidential business information that has value because it is not generally known. |
| Does a customer list count as a trade secret? | It can, if it is non-public, commercially valuable, and your company took real steps to keep it confidential. |
| Is an NDA enough to protect trade secrets? | Usually not by itself. Courts also look at access controls, internal policies, training, and how the business handled the information in practice. |
| Can a former employee use general skills after leaving? | Yes, general skill and experience usually remain with the employee. What they cannot use is protected confidential information belonging to the company. |
| Can I sue in the U.S. if the misuse happened in Canada? | Sometimes, but filing in one country does not guarantee a quick or effective result in the other. A U.S. injunction may still need separate enforcement steps in Ontario or another province, and the reverse problem can arise with Canadian orders affecting U.S. operations. |
| What should I do first if I suspect theft? | Preserve evidence immediately, secure accounts and devices, avoid a rushed confrontation, and get legal advice before key data disappears. |
A common failure point is timing. A founder learns on Monday that source code was copied to a personal drive in Toronto, then finds out on Tuesday that the contractor is working with a U.S. competitor. By then, the legal problem is no longer just about confidentiality. It includes evidence preservation, employment or contractor terms, forum selection, emergency relief, and whether a court order from one side of the border will have practical force on the other.
Trade secret cases are usually won or lost before the statement of claim or complaint is filed. The businesses in the strongest position can identify the specific information at issue, show who had access, and produce signed agreements, system logs, and a clear record of internal controls. Cross-border companies need one more layer. They need contracts and incident plans built for the reality that witnesses, servers, employees, and assets may sit in both Canada and the U.S.
Mayo Law advises companies on cross-border business matters involving contract structure, risk review, and dispute planning where confidential information may be exposed.
How Mayo Law Can Help
Mayo Law serves clients across Toronto, the GTA, and on cross-border matters between Canada and the U.S. The firm assists with business agreements, confidentiality terms, risk allocation, and dispute strategy involving operations in both Ontario and New York.
Joseph Mayo is the principal lawyer at Mayo Law, licensed in Ontario and New York, with a Master's degree from NYU School of Law. He advises clients on business law and cross-border matters across the GTA and between Canada and the U.S. Learn more on Joseph Mayo's profile.
For procedural and legal framework references, businesses can also review the Defend Trade Secrets Act through the U.S. Code, Ontario court resources through the Ontario government, and lawyer licensing information through the Law Society of Ontario directory.
This article is for informational purposes only and does not constitute legal advice. Every situation is different. Consult a licensed lawyer about your specific circumstances.